What does this mean and why should I care?
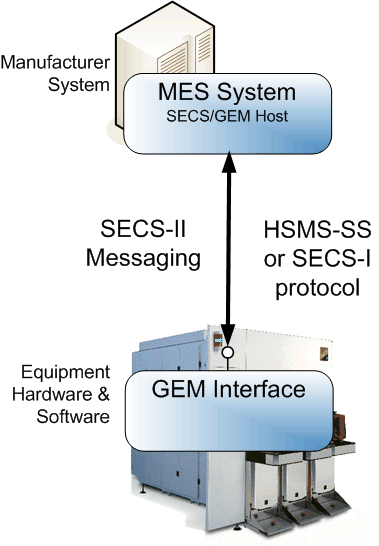
The SEMI standards for 300mm Semiconductor Manufacturing Equipment can be an overwhelming burden of information to understand, let alone implement.
The GEM standards comprise over 450 pages of documentation: E4, E5, E30, E37, E37.1, E172, E173.
The 300mm standards add another 280 pages: E39, E40, E87, E90, E94, E116, E157, E148.
And the EDA standards pile on an additional 480 pages: E120, E125, E128, E132, E134, E138, E164.
That’s over 1200 pages of standards documents filled with requirements and implementation information.
On top of that GEM and EDA collect data differently from the equipment. See a post we did on data collection for more information on those differences.
Implementing the requirements defined in those standards without an SDK would be a very brave undertaking. Even with SDKs for the standards, it would be a fair amount of work, when all you really want to do is get your equipment automated.
In addition, it is very important that those standards be implemented correctly in order for your equipment to be smoothly integrated and accepted into each fab. Different fabs use the standards slightly differently or have additional requirements. This requires experience.
GEM300 and EDA standards implementation is a very large burden.

So what does this mean?
One of the large tasks for the EDA standards is defining a hierarchical model of the equipment and what data it can produce in XML per the schemas defined in the standards. Creating the initial model and keeping it up to date as the equipment evolves is a tedious task. In addition, that model must be conformant to the E164 standard (which has over 10 pages of requirements on its own). See our blog post on conformance testing. CCF does this for you, producing an E164 compliant EDA model in the background based on your CCF programming. See our blog post on CCF dynamic model creation further details. CCF also builds the GEM interface model for you at the same time.
Further, CCF is completely GEM compliant and 300mm compliant, using the Cimetrix CIMConnect and CIM300 products which have been successfully deployed in every 300mm fab around the world on many different equipment types.
Twelve hundred pages of standards, compliantly implemented, at no additional effort. That is what this means.
Turn that donkey into a goat and use CCF.
To learn more about CCF, visit the CIMControlFramework page on our website!