Note: this will be the last blog published on cimetrix.com. For all future blogs, please visit our blog on PDF Solutions website.
Background
The SEMI North America, the Information & Control Committee meets three times per year, but this year the schedule is changed due to the SEMICON West biennial relocation to Phoenix beginning this year. SEMI held summer meetings in North America on June 2-4 at SEMI headquarters in Milpitas, CA. Like usual, the meetings are hybrid where attendees can join in person or remotely. The first two days are task force meetings including the GEM 300, ABFI (Advanced Backend Factory Integration), GUI, CDS (Fab & Equipment Computer & Device Security ) and DDA (Diagnostics Data Acquisition) task forces with Cimetrix task force leaders. The third day is the committee meeting where final decisions are made (usually) based on task force recommendations. This is a summary of what happened in some of the task forces and the committee meeting.
Note that all ballots that pass in the committee are still subject to a final review by the global SEMI Audit & Review committee, where a ballot technically can still fail when proper SEMI procedures and regulations are not strictly followed. This is rare in the North America Information & Control Committee but can happen and has happened.
A SNARF is a Standards New Activity Report Form. Before a task force can submit a ballot proposing a new standard or to modify an existing standard, the SNARF for this work must be approved by the technical committee.
Note that SEMI publishes a website with all global committee information where anyone can peruse the extensive details. It is at this website: https://www.semi.org/en/products-services/standards/developing-technical-standards.
Leadership Changes
Several leadership changes were approved during these meetings. For the last several years, Brian Rubow has been vice-chair of SEMI North America (NA) RSC Organization. During the NARSC meeting, Brian was nominated as co-chair. Alan Weber was nominated as co-leader of the Equipment Data Publication task force and co-leader of the Fab & Equipment Computer & Device Security Task Forces.
GEM 300 Task Force
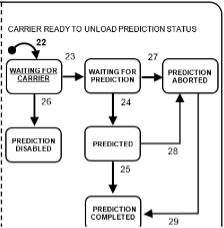
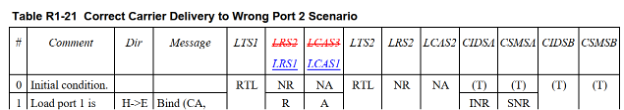
Several weeks prior to meeting, Brian submitted a SNARF to the GEM 300 task force members for review. The SNARF proposes developing a new standard that enables secure GEM interface communication using gRPC technology and TLS. The new standard would be an alternative to the existing SECS-I and HSMS protocols used today. Neither of today’s protocols are secure and therefore present a cybersecurity risk. Feedback on the proposed SNARF indicates clear approval that we need a secure GEM protocol. However, the means to achieve security is still up for debate. Alternatives to gRPC offered by task force members include HTTP/2, WebSockets and secure TCP/IP communication. We discussed this a little at the task force meeting and plan to start meeting regularly to discuss and debate the alternatives until a technical solution is selected. We also decided to postpone approving any SNARF for this work until we decided on a technical direction. The addition of a secure protocol will be the big improvement to the GEM standard. Anyone interested in this topic should join the North America GEM 300 task force. The task force approved to work on ballots to modify the well-known implementations in four standards, E30 (GEM), E40 (Process Job Management), E87 (Carrier Management) and E90 (Substrate Tracking). In GEM, we wish to clarify the well-known naming for the Processing State Model collection events. Since every equipment can implement a unique Processing State Model tailored to its operation, the number and name of the Processing State Model collection events vary. We expect each of these ballots to be relatively small. The task force is also working on another ballot (7345) for the E90 (Substrate Tracking) standard related to batch processing. The current E90 standard is unclear how to report when batches are assembled and disassembled. The batch location state model has contradictions between the batch location states OCCUPIED and UNOCCUPIED and the transition tables. The ballot proposes a solution to the contradiction and additional collection events for batch assembly and disassembly. This ballot is ready for review by task force members and will be submitted for voting in the next voting cycle.




 Earlier this quarter (16-18 April 2024) Alan Weber and Jon Holt were privileged to deliver the 3-hour tutorial that always precedes the opening session of the annual European Advanced Process Control and Manufacturing (APC|M) Conference. This year’s conference was held in Hamburg, Germany and again co-located with the Smart Systems Integration (SSI) Conference and attracted more than 200 participants across the industry and around the globe.
Earlier this quarter (16-18 April 2024) Alan Weber and Jon Holt were privileged to deliver the 3-hour tutorial that always precedes the opening session of the annual European Advanced Process Control and Manufacturing (APC|M) Conference. This year’s conference was held in Hamburg, Germany and again co-located with the Smart Systems Integration (SSI) Conference and attracted more than 200 participants across the industry and around the globe. In a slight break with tradition, rather than diving deeply into one or two APC-specific technologies, Alan and Jon took a broader perspective, covering a wide range of topics that are germane to production implementations of APC and related advanced manufacturing applications. The rationale for this approach is that APC can no longer be considered a standalone suite of applications, but an integral part of an increasingly complex factory information and control system. As a result, APC practitioners should have at least a working knowledge of these necessary complementary technologies.
In a slight break with tradition, rather than diving deeply into one or two APC-specific technologies, Alan and Jon took a broader perspective, covering a wide range of topics that are germane to production implementations of APC and related advanced manufacturing applications. The rationale for this approach is that APC can no longer be considered a standalone suite of applications, but an integral part of an increasingly complex factory information and control system. As a result, APC practitioners should have at least a working knowledge of these necessary complementary technologies.